BGINFO - A Posh Recreation
Recently I have been building a lot of Windows Servers in different environments - one
Just a very brief blog post regarding the power of grep and icat in relation to forensic images. I am currently revising for my GCFA certification and as part of this revision was looking at the creation of timelines both the filesytem based timeline and the super timelines.
I am the first to admit that I like a good GUI and tend to currently spend a lot of time in that kind of environment but I have heard on many occasions the power of the command line from people in the industry I have come to respect such as Kev The Hermit and Chad Tilbury. So I thought I would take some time out to look into how a couple of tools available within the Sleuth Kit contained in the SIFT workstation might help me with very quick triage of an acquired image.
For the purposes of this blog post I am going to find and extract the System event log (SysEvent.Evt), I will be doing so from an image I have previously created within my VM lab which I was using to research document exfiltration from a system, I created the image using the well known FTK Imager Lite.
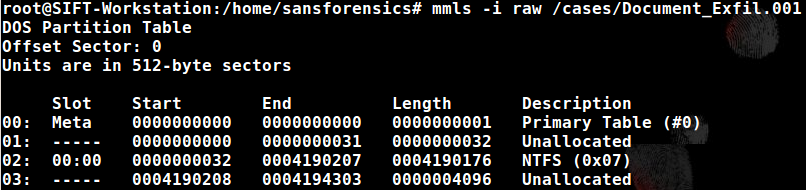
For some of the commands I will use I will require the offset for the partition within the image so for this I will run the mmls command as follows:
 |
| -i is used to specify the image type and in this case it is a .001 (dd) image. |
We can see that the NTFS partition in this instance starts at sector 32 which we will use in the commands that follow.
Now I want to use the grep command to find the event log inside the image:
 |
| -r = Recursive through directories -F = Will display only files -o = This is where we put the offset for the partition -i = makes the grep search case insensitive |
Now we have found the event log of interest we are going to use a tool found within The Sleuth Kit called icat to export this file so that we can then view it within our tool of choice for event log analysis. To do this we will need one important piece of information which is the inode for the file. We already have this information located within the screenshot above. The inode location which we require is 4381.
This command locates the file within the image and copies it out to the location we have specified. I was then able to export the event log and open it with my favoured tool which is Event Log Explorer:
So my journey along the world of command line continues!