BGINFO - A Posh Recreation
Recently I have been building a lot of Windows Servers in different environments - one
Grumpy Admin here, yes it is me!
Apologies for like just going 404. The day job has taken up a lot of my time recently, and a lot of my time has been on non-windows systems and documentation and design and security work. This combined with a young growing family and some excellent films being released. Has resulted in a lack of time dedicated to Windows, Powershell and blogging in general. So I thought, I would do a simple blog/product review on the New Microsoft Windows Admin Centre (WAC)
I have to admit, it an exciting time to be in the Microsoft Sphere! There a trend of opensource and cross-platform support for products like MSSQL and Powershell.
The good news, I have a couple of small work projects, that will be using a lot of Powershell, so I expect there will be an opportunity to blog on PowerShell.
In the interim, I am acutely aware that I am getting rusty and stale on the blogging front, and the site visit count if going south like facebook subscribers who value their privacy!
There was a recent product release from Microsoft, which seems to slip by some administrators, I played with the beta, and when the release version came, I grabbed it and threw in our system centre store.
I am frequently and continuously reminded of the fact that many professionals don’t keep their skills up to date, is watching a webcast or reading the register too much hard for some people!
Anyway, I decided I might as well write a quick blog and give people a tour of this new tool.
What is this new tool I hear you asking? Yeah, it has been an out a little bit so any decent professional would off read about or played with it! It was featured on the Reg a while back!
Well, it is nothing other than the new windows administrator centre, a new excellent new shiny graphical user interface for managing Windows servers. However, there is a small twist. It an HTML5 interface that you access through a web browser.
Now the first to stress this isn’t a replacement for other traditional management tools, but a tool to complement their usage. However, it does an excellent job of consolidating common tools and from my brief experience is helpful for getting simple performance metrics and doing quicks stuff.
As the Microsoft documentation states, it complements not replaces.
So let’s have a little look at this fantastic new tool from Microsoft. Grumpy Admin seems to be in such a good mood today!
First, we need a server infrastructure to play on. So I shall quickly set up an Azure Domain with the following:
This setup will demonstrate how the tool works across what is currently deployed across my company infrastructure and will highlight any problems that I find with the tool. Grumpy Admin requires from plausible excuse to be doing this in work time right?
I will require a client to run this new tool on as well. So a Windows 10 machine will do! On the management front, I did read somewhere that there is no planned to support the management of Windows Clients lower than Windows 10. But would you really want to use this tool to manage clients? Everything about this product is screaming server management!
Now with the Windows Administration Center, there are a few “deployment options” to consider, and think about.
You can install it on a domain client, a local Win10 client.
It can also be installed directly on a server as if it was a local client.
Can be installed on a gateway server and access from a client browser.
There is also an elegant HA solution with this product. If you are using it to manage computers, you want the tool you use to be highly available!
The Windows Admin Center product has this baked in from the beginning, and I think that is a neat and significant step in product design from Microsoft! Grumpy Admin approves!
So for this little trial of this new tool, I am going to install on a Client, I will also install on a server to try the “gateway” mode.
There are also some reliance and dependencies to consider, for example, you have to have the Windows Management Framework version 5.1 installed.

Now 5.1 come baked into Windows Server 2016, so to manage anything lower. You will have to install the WMF 5.1. However, Grumpy admin recommends you install this framework regardless.
So I get the correct dependencies installed in my little lab environment, and I’m ready to rock…
Dependencies do make Grumpy Admin grumpy; an installer really should have all the bits it needs to run the core program! I don’t mind, but the dependency checked, should at least give you download links or better yet include the dependencies in the installer. Yes, this could mean your installer is more substantial than it should be but we all know Grumpy Admin is lazy, why make me do more clicks than required?
A recent example of dependency hell would have been when I had to add a new management pack into Microsoft SCOM the other day. Wow – that software product is very needy and is more grumpy than Grumpy Admin! Almost on par with the Microsoft DPM product! System Center is the needy Girlfriend of the Microsoft Product range!
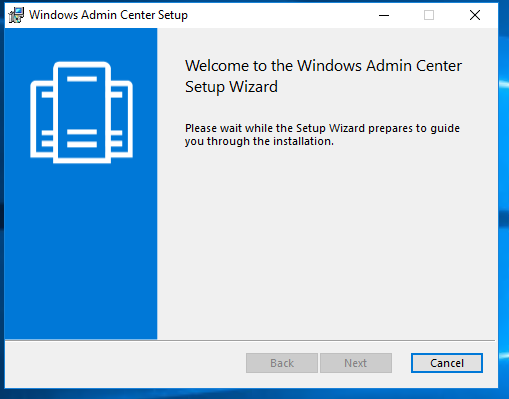
Now that all is set let’s start off by installing it on our 2016 Server.
The first few next’s are standard;
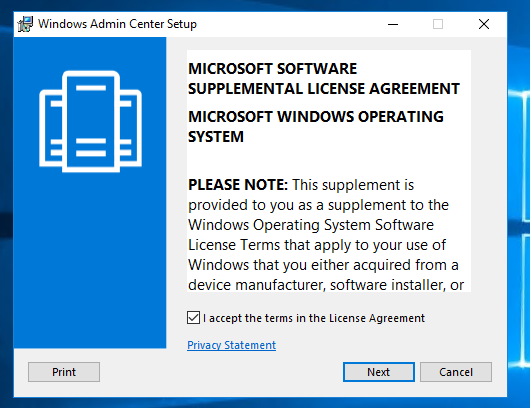
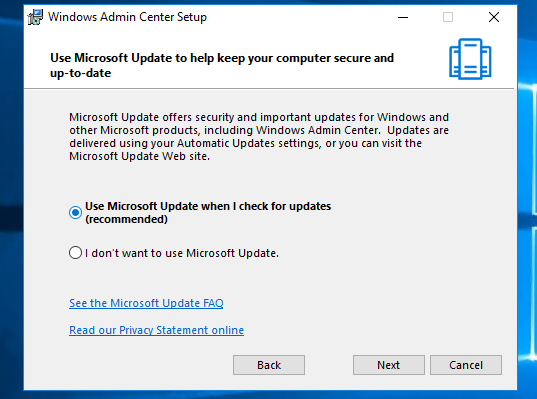
then we get a choice – Does this mean Windows Admin Center is now in WSUS? Well, the answer is yes. Microsoft will be pushing updates to this product via Windows Update / WSUS
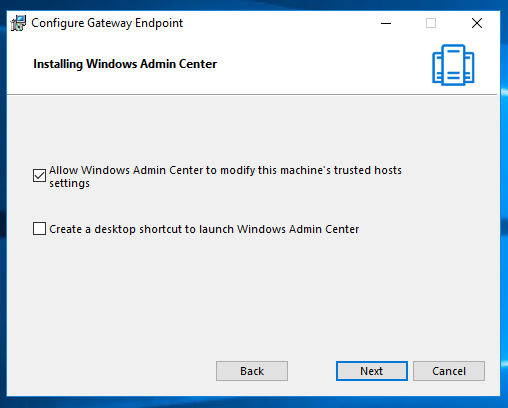
The next page is an not so exciting consent page – allow Windows Admin Center to modify this machine’s trusted hosts settings. I think we know where we see this sort of thing before, it’s nothing to be concerned, and it’s how remote management works in Windows WRM and Powershell Remoting.
Ah – this next screen is music to my ears! It looks like SSL is by default – Not an afterthought, this makes me so much less grumpy. It looks like the Secure by Default and Design principle has started to hit home!
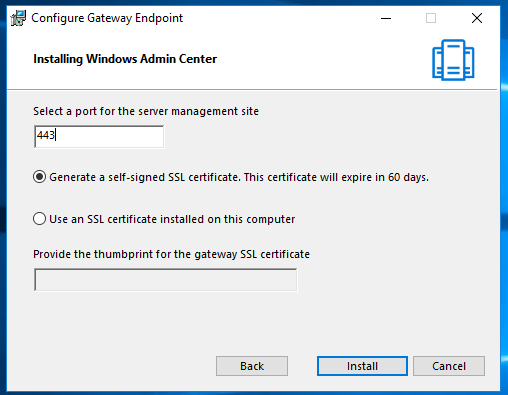
However, there is no way on this earth any engineer/programmer building a remote management tool would do so with HTTP and then bolt on SSL/TLS as an afterthought! It’s 2018 people!
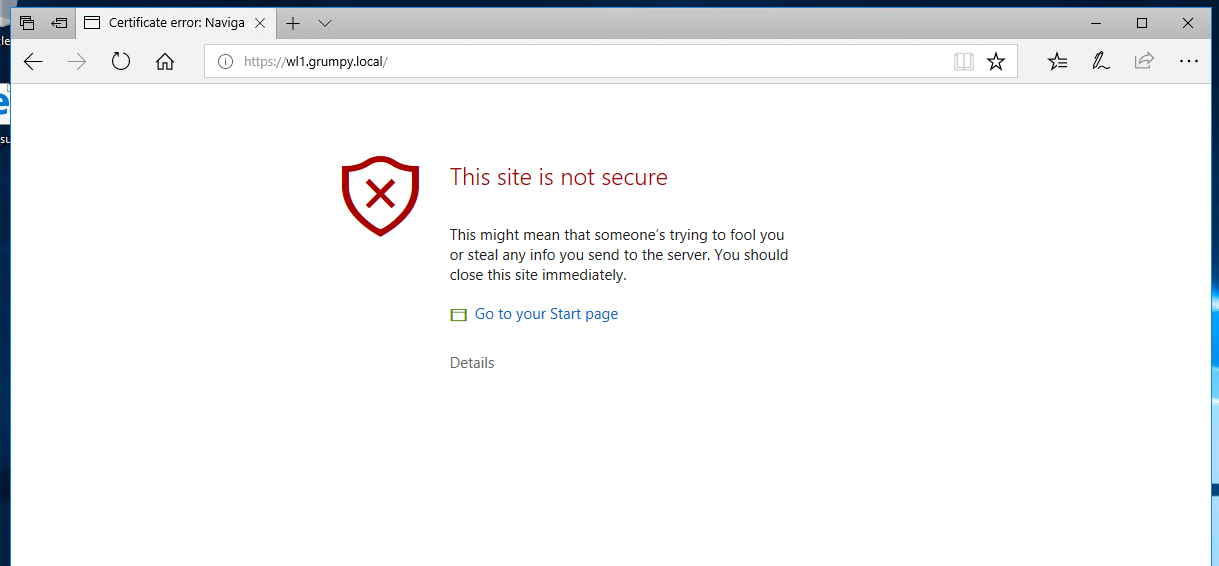
Certificate wise. I will have to accept the Self-sign certificate, for now; I’m not going to set up a LetEncrypt or private PKI just for this build. Remember, Grumpy Admin is lazy!
Another thing, this server doesn’t have IIS installed as a server role. Does this product use IIS or has Microsoft moved away from using IIS in their products? Let’s get it installed, and let’s have a poke around the install directory to see if we can find some clues to how it is working under the hood!
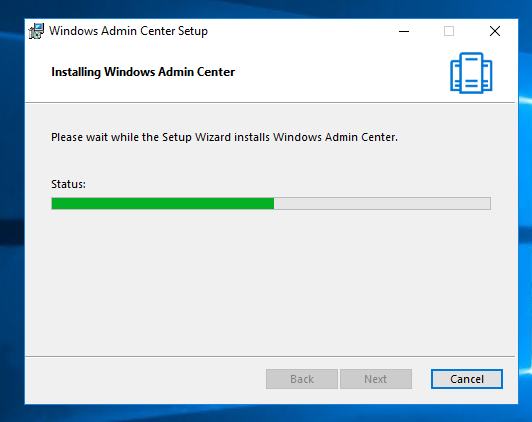
Another point to note, while we are watching a green progress bar is the official documentation.
The old Internet Explorer isn’t supported! Why am I mentioning this! Well, if you install it on a server install of Windows 2016. Where is Microsoft Edge? It doesn’t get installed does it, leaving Internet Explorer as your browser.
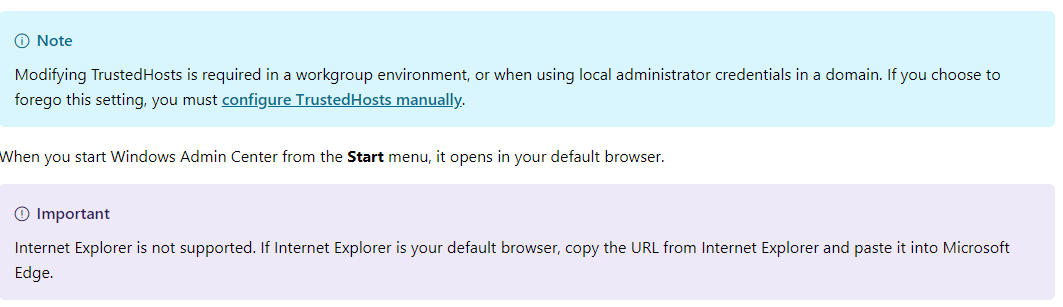
So we will have to use a client to access the page or install a compatible browser to use the product.
Now back to poking around the Windows Admin Center software installation directory, you can always tell a lot about a program by what dynamic linked libs and files are hanging around in its installation folder.
Let’s have a look and see what we can find out about this product from the files in that directory.
Most administrators who have worked with Windows and Web service what this highlighted file is
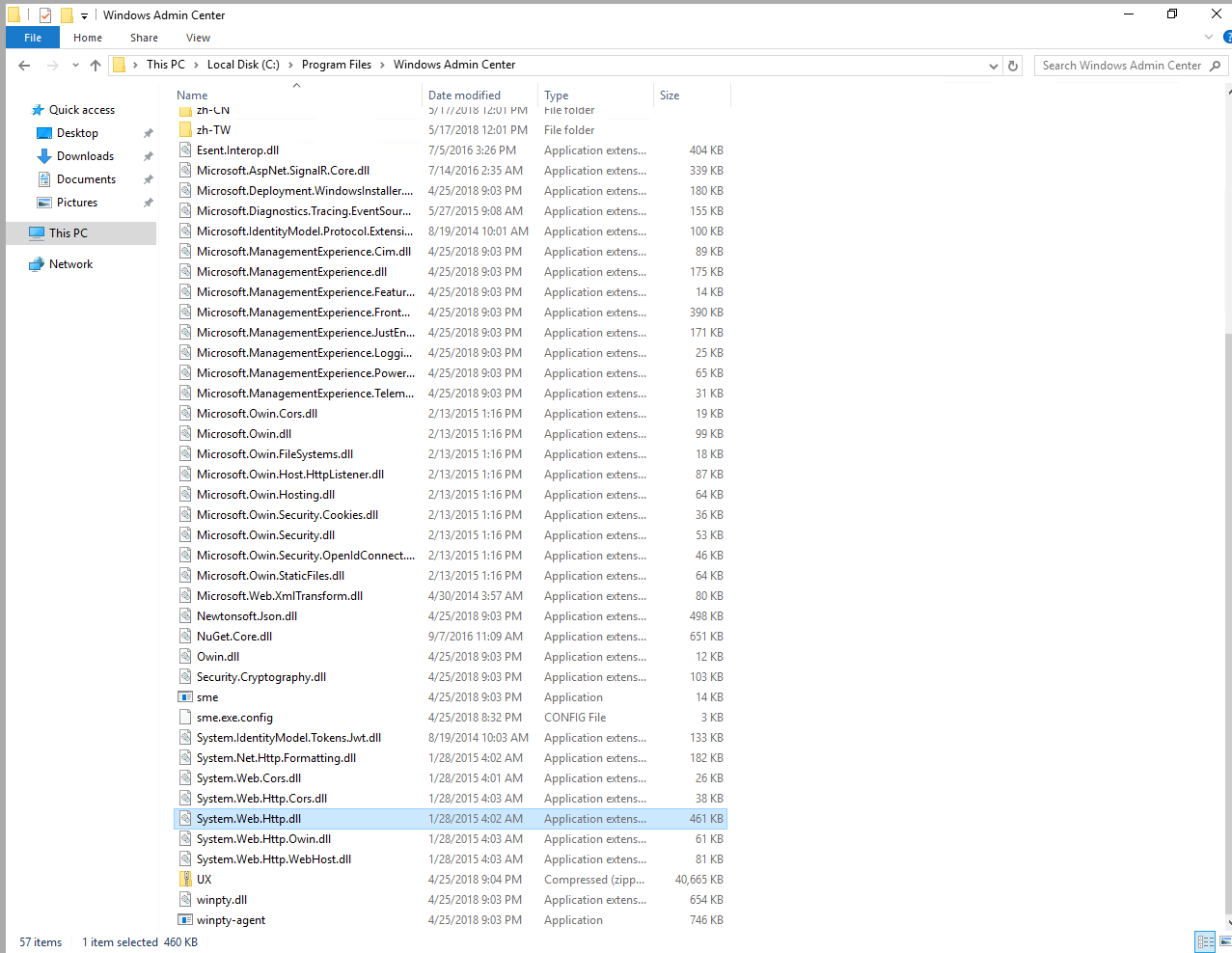
system.web.http.dll
It is Microsoft core HTTP dll – gives access to the web HTTP namespace useful for PowerShell and C# etc. So it looks like the web server is built in an independent or whatever web server versions are. Running. Not using IIS, Could be useful to know, for future exploitation maybe?
There is a zip file called UX. Which must be the User Experience/interface stuff… let’s open it and have a sneaky peek!
Now there some HTML and javascript files, and more important and useful to me is modules and Powershell… but to be honest, I’m going down a rabbit hole here and moving off point of this blog, but we are starting to get a feel of this application. Also, we have somethings we can loop back to and think about and maybe an experiment. Things like, are they secure signing their javascript files?
Could a nasty person, modify the files, insert a backdoor a dropper and get access to servers through the tool? Might be fun to have a look at in a future blog post.
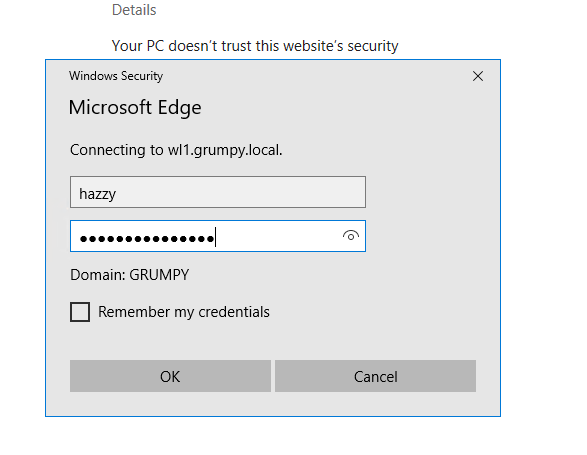
Lets login to our client that has the Microsoft Edge browser installed and connect to our URL and see if we can access the Windows Admin Center for the first time! Are you excited?
I navigate to the URL of the Windows Admin Center installation, and as expected, there is the SSL certificate warning.
The site also prompts for credentials, which is a good thing! Then we are in!
I close the welcome screen; we don’t need a tour, we are the keyboard cowboys, we don’t need tours or to RTFM do we now?
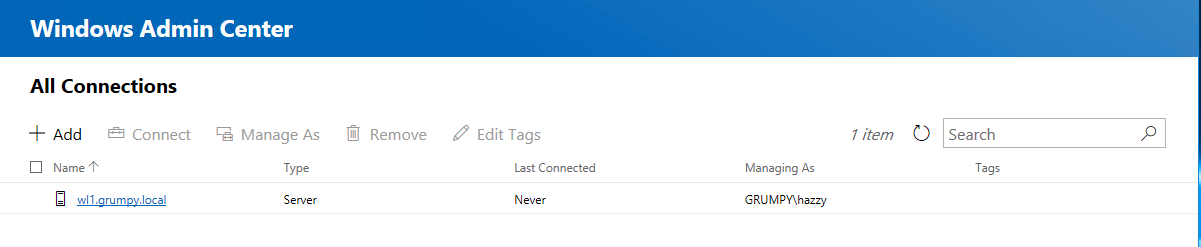
I can see we already have a connection – to the server, that it is installed on, but what about the rest of them in my environment?
I select the “Add”, and naturally, we want a Server Connection, so the flow seems to be logical and well designed!
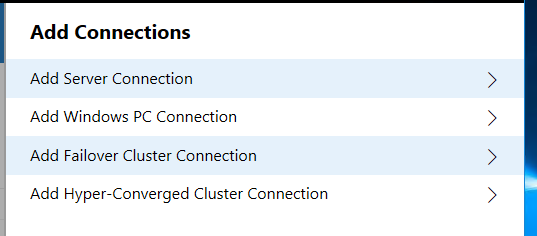
At this point, we can either add manually or import. I wonder does the import query AD? No,, the quick answer is it seems to require a txt file of computers!
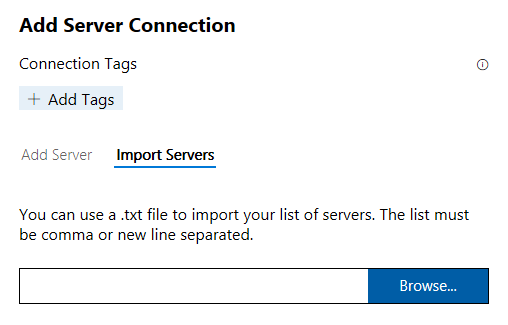
So typically, I would go for the FQDN – but I have DNSdns working, so let’s see if typing in DC1 and let’s see if it gets there!
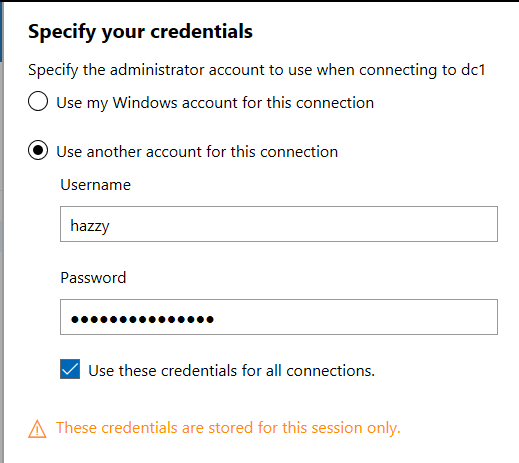
Grumpy Admin click connects and it prompts me for credentials. I tick the Use these credentials for all connections. I like the idea that credentials can work for a whole session only, this seems a good thing again highlighting the secure by design principles
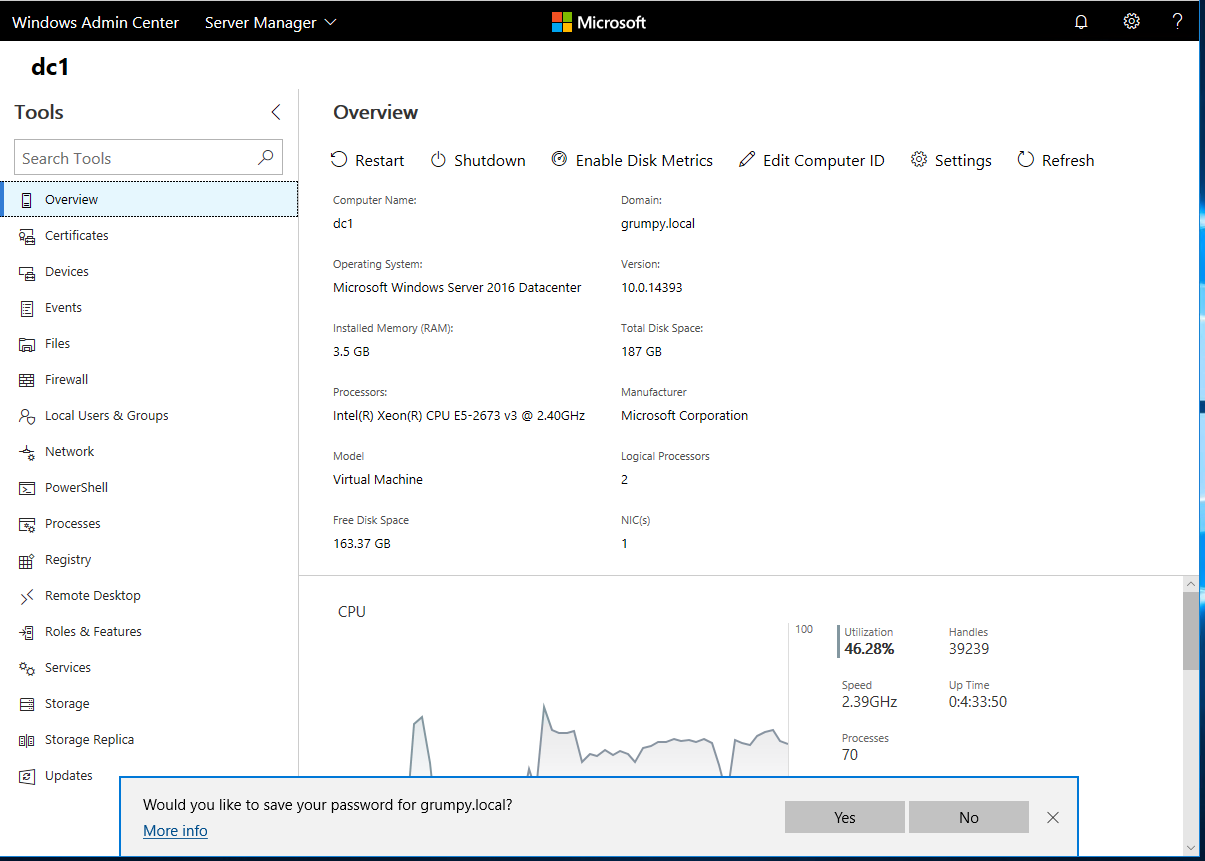
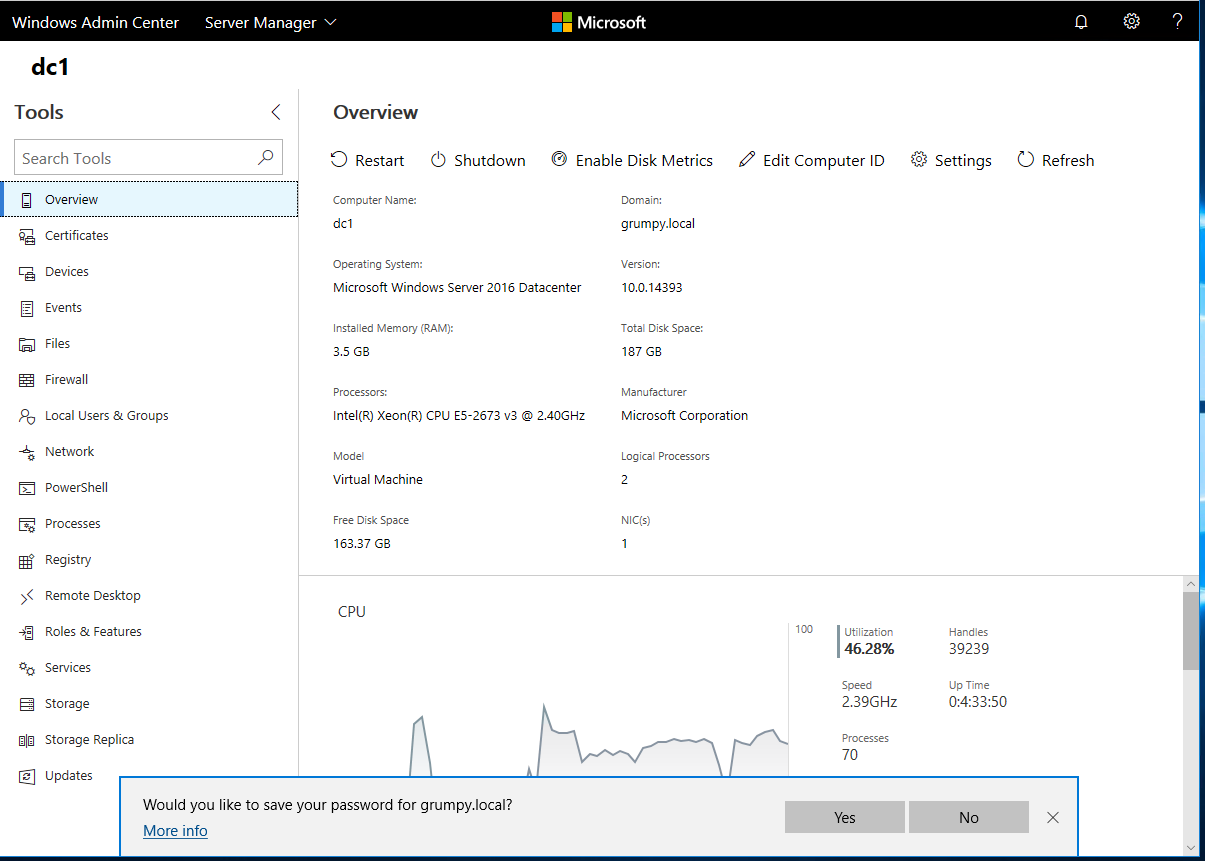
It works and gets there! Grumpy Admin must say that it looks quite impressive from the initial screen and overview. Not easily impressed but it does look polished and beautiful. Responsive and the information presented is kind of useful.
Let’s get to the meaty useful stuff; lets hit the PowerShell button
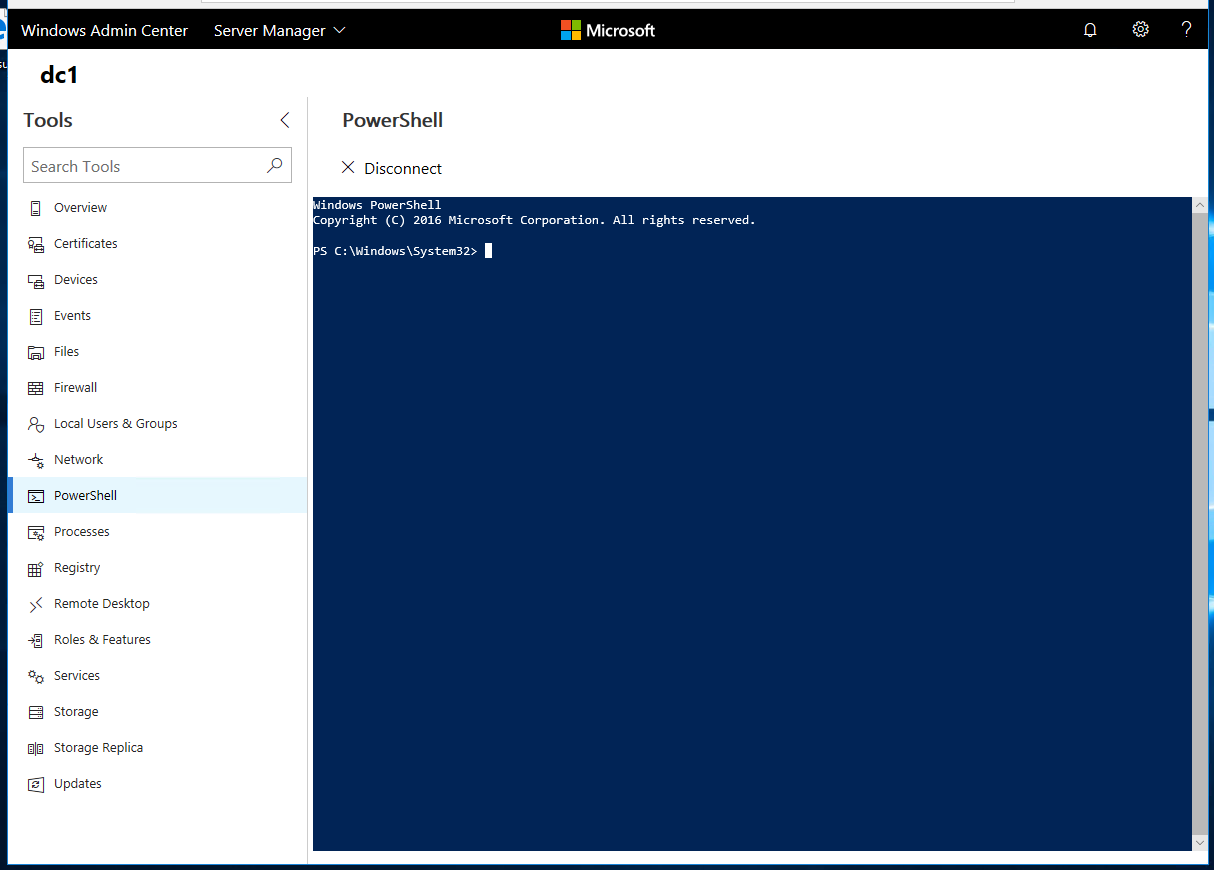
Wham! I have PowerShell – This is all I need really! I’m almost sold on this told right now due to this feature!
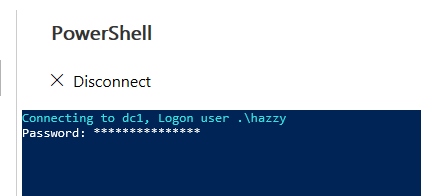
It launches a local PowerShell in the window, and then it seems to PowerShell remote in from there! Saves me a bit of typing! There are plenty of other features to have a look at. I quite liked looking at the metrics, and I think there is something cool and exciting to be down with the metrics in the near future.
All in all I think this is a great tool, and Windows Server 2019 will come with it preinstalled if what I have been reading is correct. This will be good addition to any administrators tool kit!
So why not download it today and have a play! This sort of improvement in Windows makes Grumpy Admin a lot less grumpy and is an exciting step for Microsoft, this brings in some real high hopes for Windows Server 2019. Watch this space! My testing with the other OS didn’t throw any problems.
Also if you want to get more information Microsoft’s own documentation is good, there is also a good series of youtube videos on WAC.