BGINFO - A Posh Recreation
Recently I have been building a lot of Windows Servers in different environments - one
Good News,
UPDATED: check https://hazzy.techanarchy.net/nano/file-copy-session-improvements/ for a better method of sending the nano01 djoin file to the nano server! 🙂
Grumpy Admin passed his CISSP exam, bad news, I have to wait to see if I get endorsed and welcome to become a CISSP! Fingers crossed, or my boss won’t be too happy! Now back to the real world of being a tech geek!
A week away without launching a single PowerShell command gave me withdrawal symptoms!
Now, before I went off to my CISSP boot camp, I was busy testing Windows Server 2016 and Nano – been playing for a while, and well the intention is to get skilled up so that I can in the 6-month window required, get some Windows 2016 server skill and certifications as well, we will need to keep our partner agreement with Microsoft.
So previously in my blog posts we deployed a Windows Nano server and had it running IIS – that great, but it wasn’t domain joined! So let’s domain join our Windows Nano server.
So I enter the Nano server with the normal Enter-PSSesion, because as you will remember, Nano server is a headless server…
and to just prove, I’m on the right machine, I do a get-computerinfo cmdlet.
Nothing makes me more grumpy than doing shit on the wrong machine – I jump between so many boxes these days it is hard to keep track! Yes the cmd prompt helps, but if you have to do a proactive read to check the machine ID before performing an operation… that can’t be bad right?
Next thing that I need to do is to configure my little Nano Server to use my domain DNS server for it’s domain look ups and this will then allow me to domain join the machine. 🙂
I can use the Powershell set-dnsclientserveraddress cmdlet here but in order to use that I really need to know the interface address, so the quickest way is to just to run a quick
get-netipaddress
This will give me the ip and the interface index,
So I can then go ahead now I know the interface ID and issue that cmdlet to give my Nano server some DNS loving!
set-dnsclientserveraddress -interfaceindex 3 -serveraddresses("192.168.12.54")
And as Grumpy Admin always likes to do, I can test this out, I can quickly ping the gh.local domain name and see if it replys 🙂 You could also use the PowerShell Resolve-DnsName Cmdlet here – but as you are more than aware, Grumpy Admin is lazy!
Then with the DNS confirmed, I am ready to domain join this machine, and I just need to enter the add-computer cmdlet and restart-computer and we are done! 🙂 God, I love PowerShell!!
add-computer
WTF! cmdlet not found – Nano doesn’t have add-computer cmdlet…. ummm ok… what to do, what to do… Grumpy Admin, does what any competent System Administrator will do in this situation and he Googles, and he discovers that he has to use the old offline join method. Really, Microsoft, Really… offline domain join! I guess this makes sense as well, really you should be deploying Nano in a scripted manner, with DSC or some other orchestration tool… The days of manually building and deploying a server are falling away…. Like the Minuets in my lunch hour!
So how do we offline domain join, well you know, that method they teach you on Server courses and test you on the exam, where you never thought you would need to use it in the real world! The old faithful djoin! This hand on heart is the first time outside of a learning lab on the tool, that I had to use this tool. Maybe, I just never meet the right situation! I had to Google the Syntax to be honest with you! I recommend you do the same
https://technet.microsoft.com/en-us/library/ff793312(v=ws.11).aspx
So initially todays post was going to be on something else, but as I was building the environment to do the post and finding out that Nano didn’t have add-computer I thought I would turn this learning experience into a post. With that in mind, I quickly did another Get-computerinfo
as you can clearly see the server is in a workgroup and is a standaloneserver.
I jump on to my domain controller for my gh.local domain, my current Windows Server 2016 test server, and there I offline provision the new machine for domain join. My little Nano server! Nano01
djoin /Provision /Domain gh.local /Machine "Nano01" /Savefile c:\nano\nano01
Excellent, no problems, the syntax is simple and I saw online examples where people have scripted it etc!
Now the next step is copy the output to our little Nano server and provision it so he can be a member of our little domain!
PS, if you are wondering, and never seen a token for domain joining before – here is is! a quick GC on the nano01 file that djoin created!
So on my 2016 AD (ok for them who are picky ADDS) Server, I create a new SMB share, where my nano01 file is ie c:\temp
Then on my Nano server, I create a new PSDrive that has that unc as the root and we will be able to access the djoin object/token to offline join the machine!
OMG! WTF twice in one day! That really should of worked grrrr…. this is starting to make me grumpy! Grumpy Admin hates it when things go wrong… Ok let’s work this out!
Let’s do a quick test-path to the unc
Ah, I must have a permissions issue, let’s try and solve that… Insert many many swear words and a quick cup of coffee! This proved to be quite frustrating, I providing credentials and everything still a no go! Used the IP etc and still nothing WTF! grr
In my trial and error and Google research, I read some guy was doing file connecting to the c$ via the old net use command! So I give that a try from my server to c$ of my Nano server!
That didn’t work – But I got an error 53
I have as I expect you have seen this error before, so that got me thinking, I jump in to my little Nano PowerShell session and run the old trusted favourite cmdlet.
get-netconnectionprofile
Bang! there we go! As expected, I had over looked something very simple! MY mistake made me even more Grumpy!
The server network card is on the Public interface, and this is quite restrictive. Anyone who has meet this before will know that you need to enable the SMB firewall rules for this work, in this zone.
So we can use again use PowerShell here, there no wf.msc to use! You could use the console, and the recovery interface to modify the network firewall rules, but PowerShell is the way forward, I like PowerShell… I might do a blog about it! Oh Wait….
So to quickly do this is fine, but it’s perhaps just wise to quickly check the name of the firewall rules, that we need to enable! Precautions are good!
get-netfirewallrule | select name
So then we can just set these two rules to “Enabled = True” and bingo bongo – problem solved!
and as proof of the pudding we can do a get-netfirewallrule to confirm!
get-netfirewallrule -name "FPS-SMB-In-Tcp"
As you can now see the enabled property is now set to True
We can now successfully map a drive to our Nano Servers c$ from our Windows Server 2016 Server- as it was the closest command in the history, when you press up and Grumpy Admin is lazy, I just use the net use x: cmdlet. After spending 20 mins working through this, I just wanted this machine domain joined so I could continue with what I was actually trying to test!
I navigate to the x: drive and I make a temp directory, this is where I will store my nano01 djoin file! and then I just do a standard copy-item command
From there we need to use the file we just copied to join the machine to the domain…
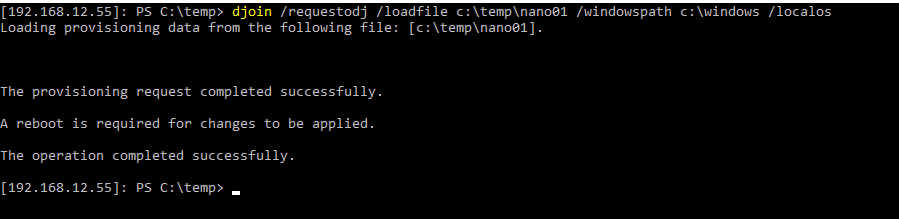
djoin /requestodj /loadfile c:\temp\nano01 /windowspath c:\windows /localos
The operation completed successfully!
Thank you! finally! grrrrr We need to throw a very quick restart-computer at it as we have just joined it to a domain, as it’s a Nano server it boots in like 5 sec’s amazeballs!
I’m always impressed… It boots so fast, I often don’t have enough time to break out of focus from my VM to activate my screenshot program! Which is like 3 keys!
then to confirm things, I just quickly enter another PSSession, this time using the FQDN of our Nano Server!
Enter-PSSession nano01.gh.local
I re-run the get-computerinfo and check the status of the server, as you know – Grumpy Admin loves to confirm shit!
As you can clearly see from this little screenshot, Nano01 is now a domain member server! Fantastic! Amazing and easy as 3.141… would be much faster if they added the add-computer cmdlet! Now Nano01 is domain joined, I can do a few things to help manage and monitor it as per any other windows servers in your environment!
I could add it to server manager, just like this – The role IIS appears because it detects it!
I could use the server manager now to manage the features of the roles installed on it! Excellent! I could even right click and restart it!
Brilliant…
Well, then enough GUI yucky stuff, PowerShell is the way forward isn’t it boy’s and girls and the bottom line is, I better get back to work, my boss keeps looking at me as if I have work to do… apparently the numbers next to the word inbox in outlook means I have mail and I should read it! Has he worked out that I never accept read receipts! bah!
Hazzy